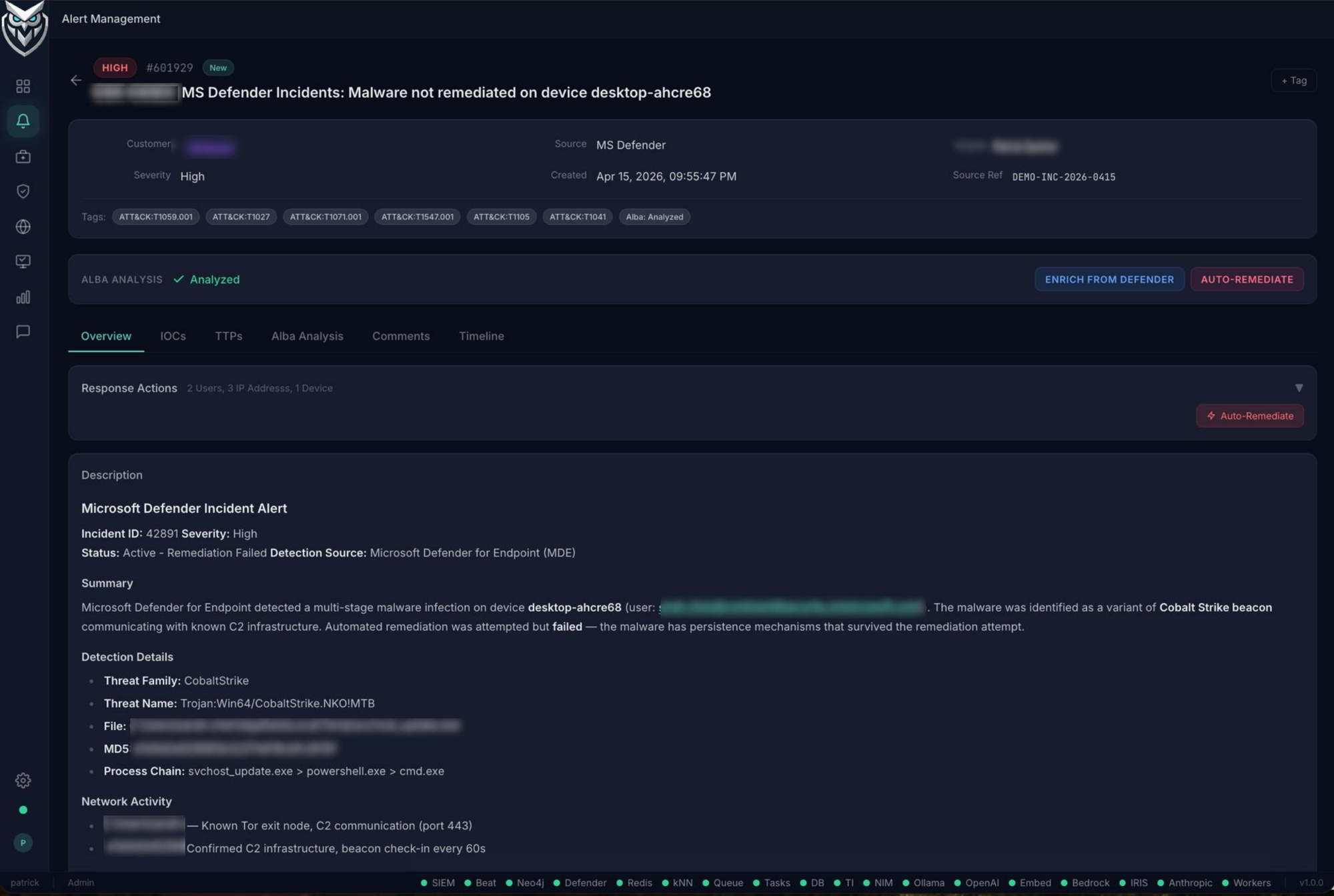
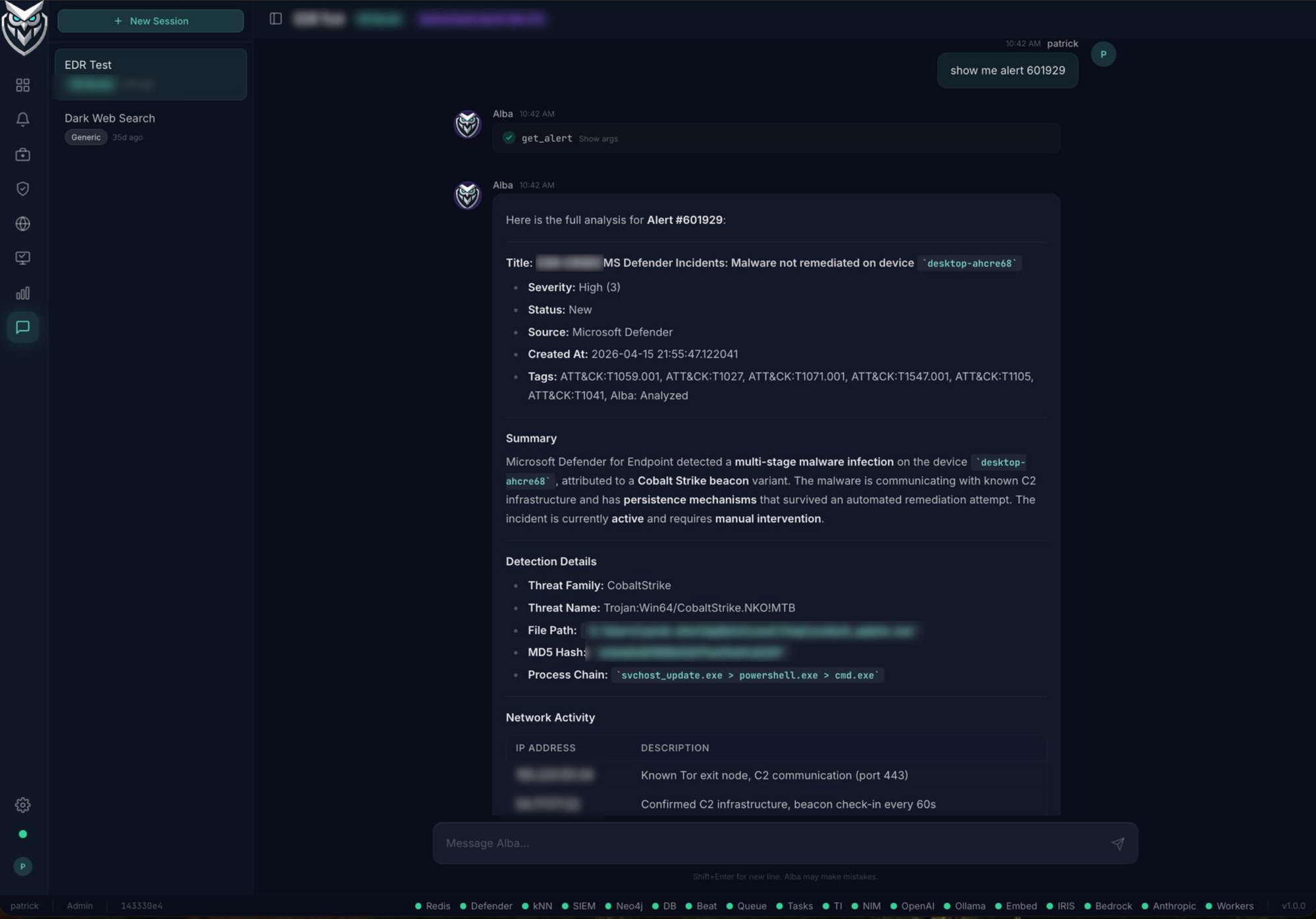
alba > analyze 555833 --depth 1
[1/7] Fetching alert from case management...
[2/7] Extracting IOCs: 12 IPs, 3 domains, 2 hashes
[3/7] Enriching via threat intelligence (400+ feeds)...
2 suspicious • 0 malicious
[4/7] History: Rule fired 47x, 94% FP rate (30d)
[5/7] SIEM depth=1: 14 queries → 10 follow-up
Discovered: 4 hosts, 2 users, 6 IPs
[6/7] Memory: 3 similar past investigations found
[7/7] Generating analysis...
✓ Classification: True Positive — HIGH confidence
▶ Isolating compromised endpoint via EDR...
✓ Endpoint isolated • Incident ticket created
✓ Posted to case management • Tagged • Indexed
62.1s total • 24 SIEM queries • 3,156 tokens
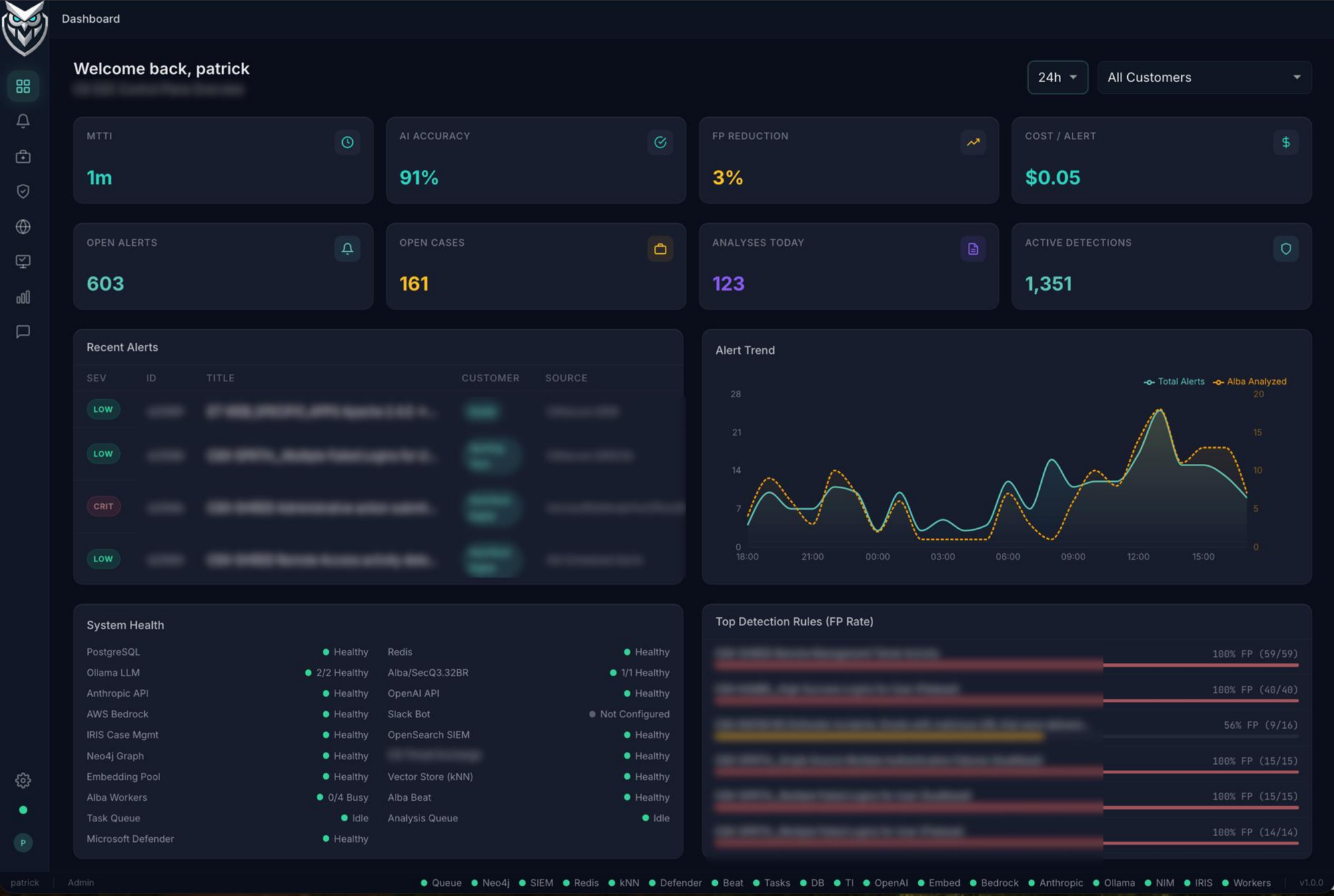
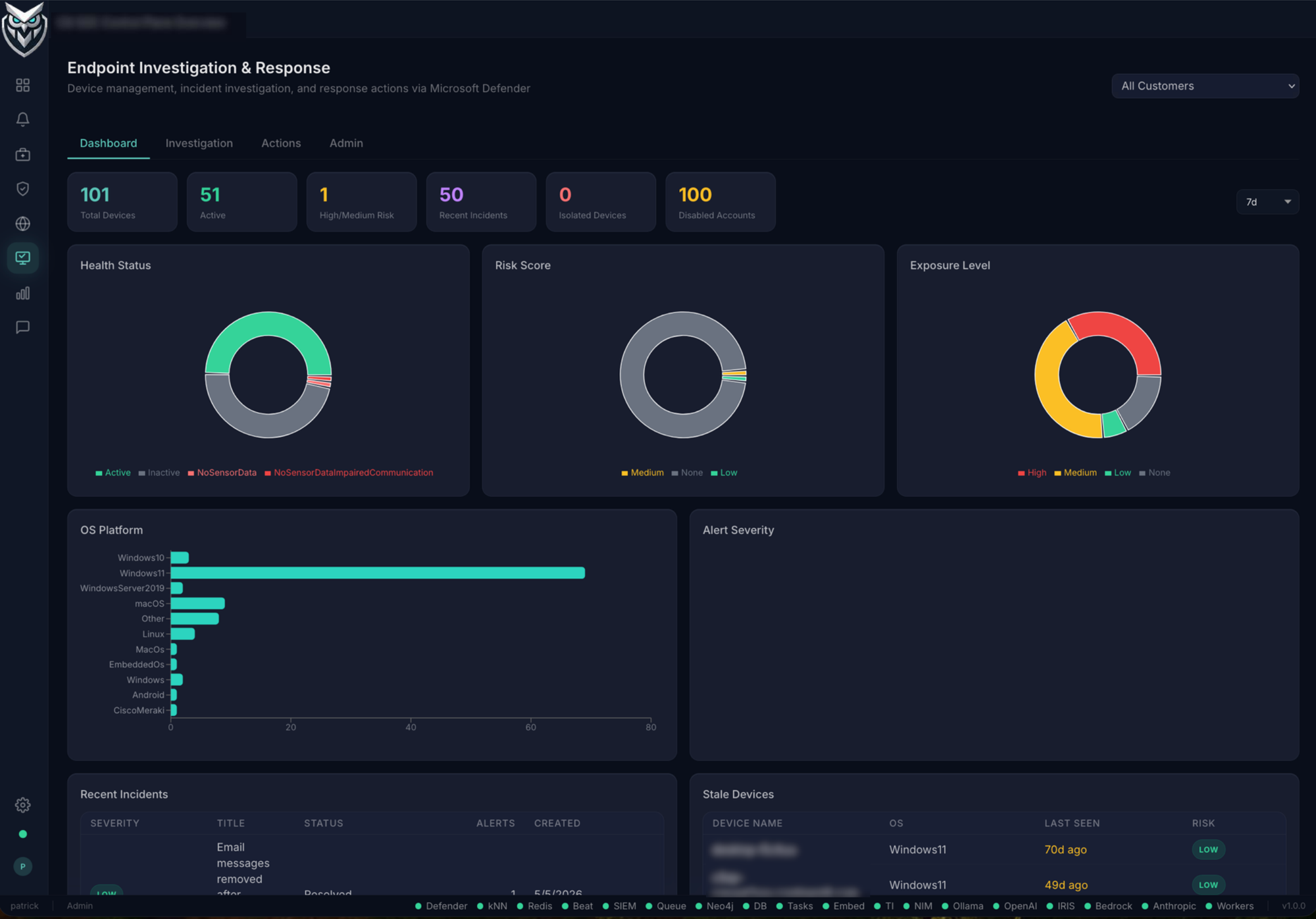
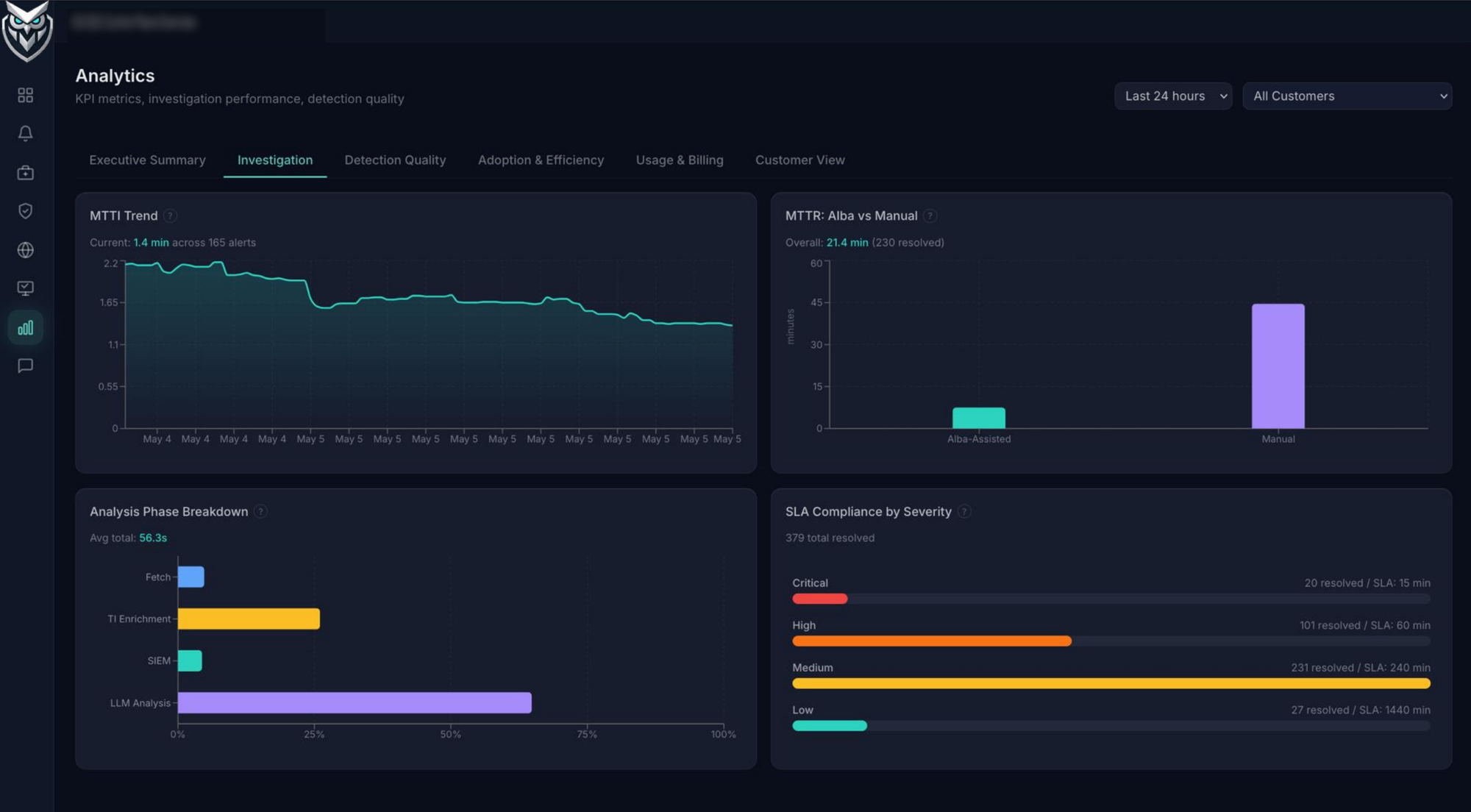
Multi-tenant SOC Control Plane
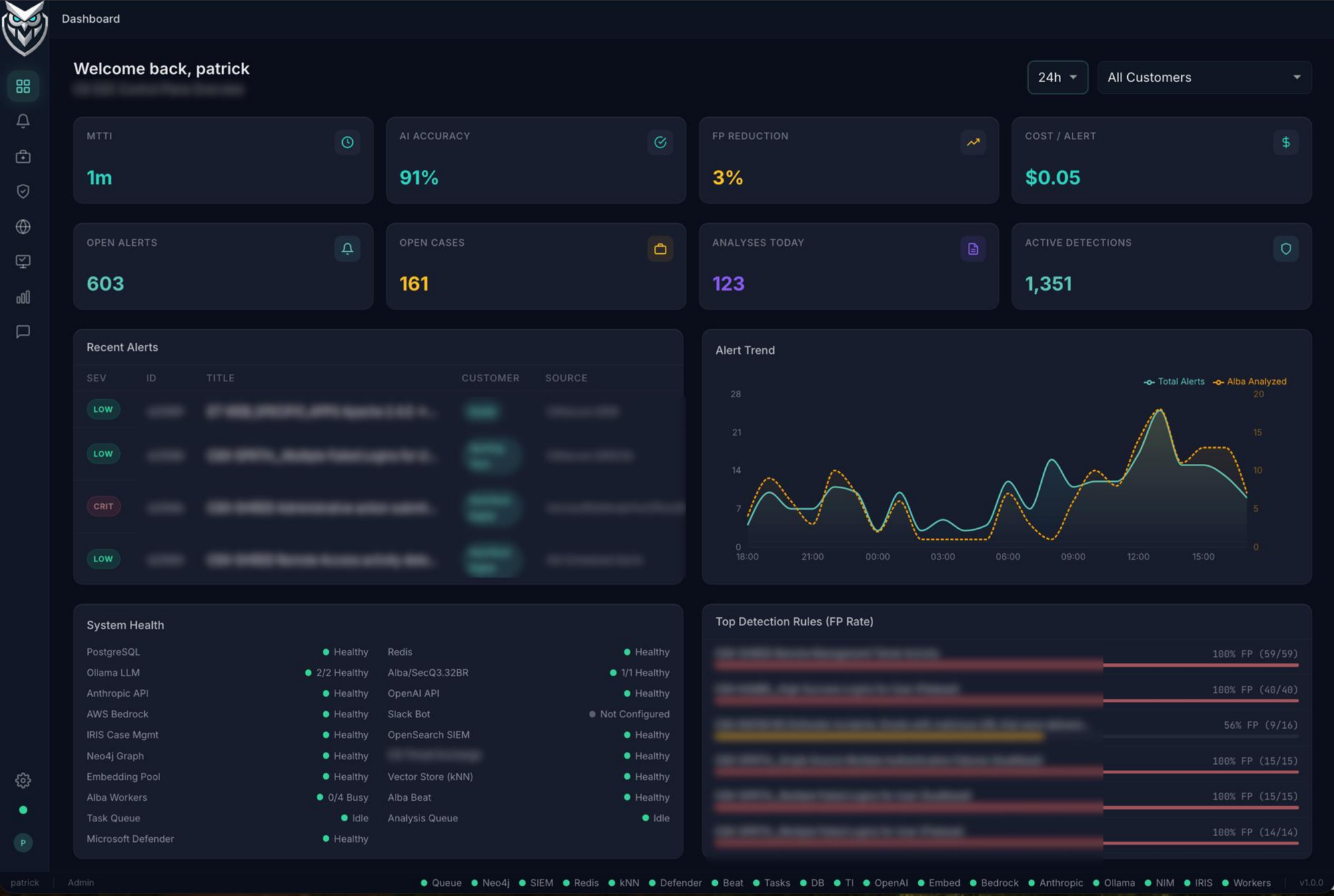
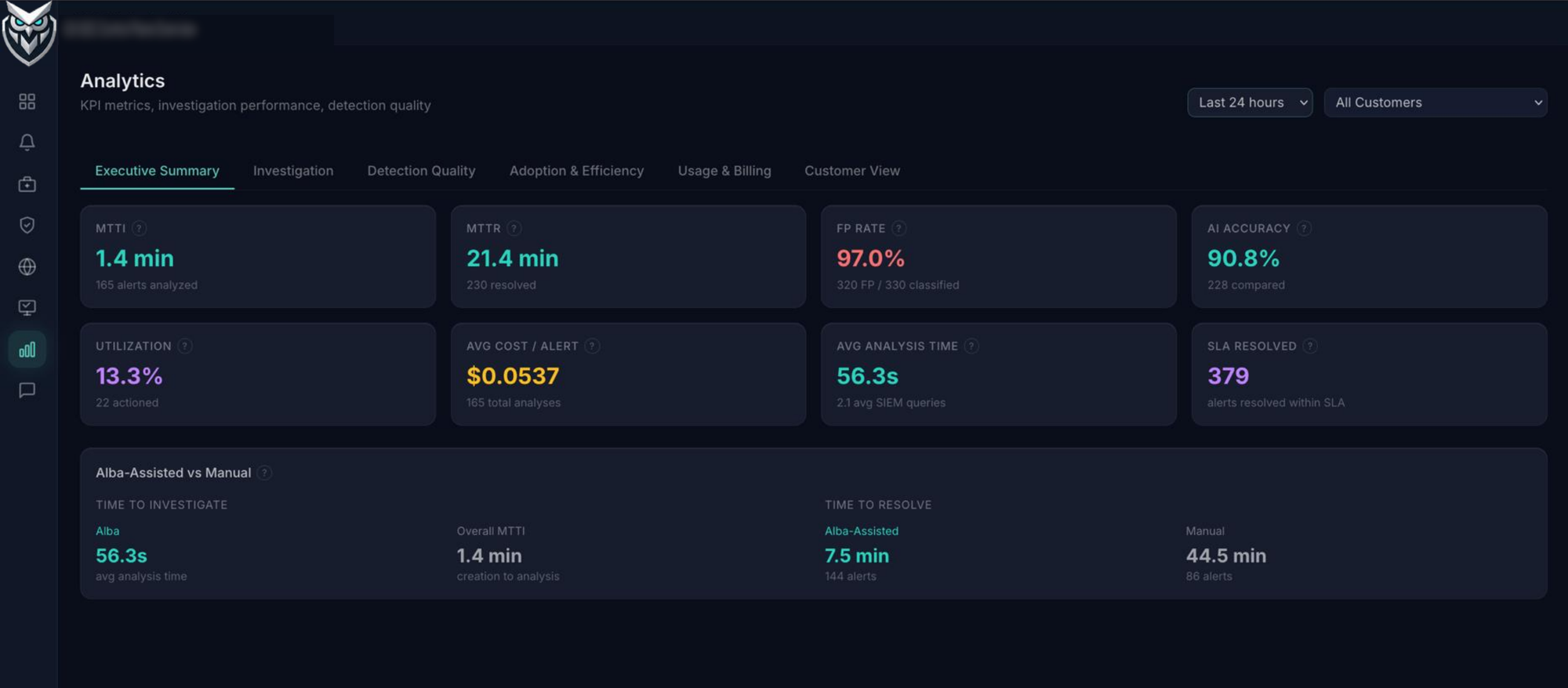
“We went from a 6-person overnight rotation to 2 analysts plus Alba. Our MTTR dropped from 38 minutes to under 4. The accuracy improvement alone justified it — our analysts used to misclassify about 1 in 5 alerts under fatigue. Alba hasn't missed one in three months.”
VP
VP of Security Operations
Global MSSP
97.6%
Classification Accuracy
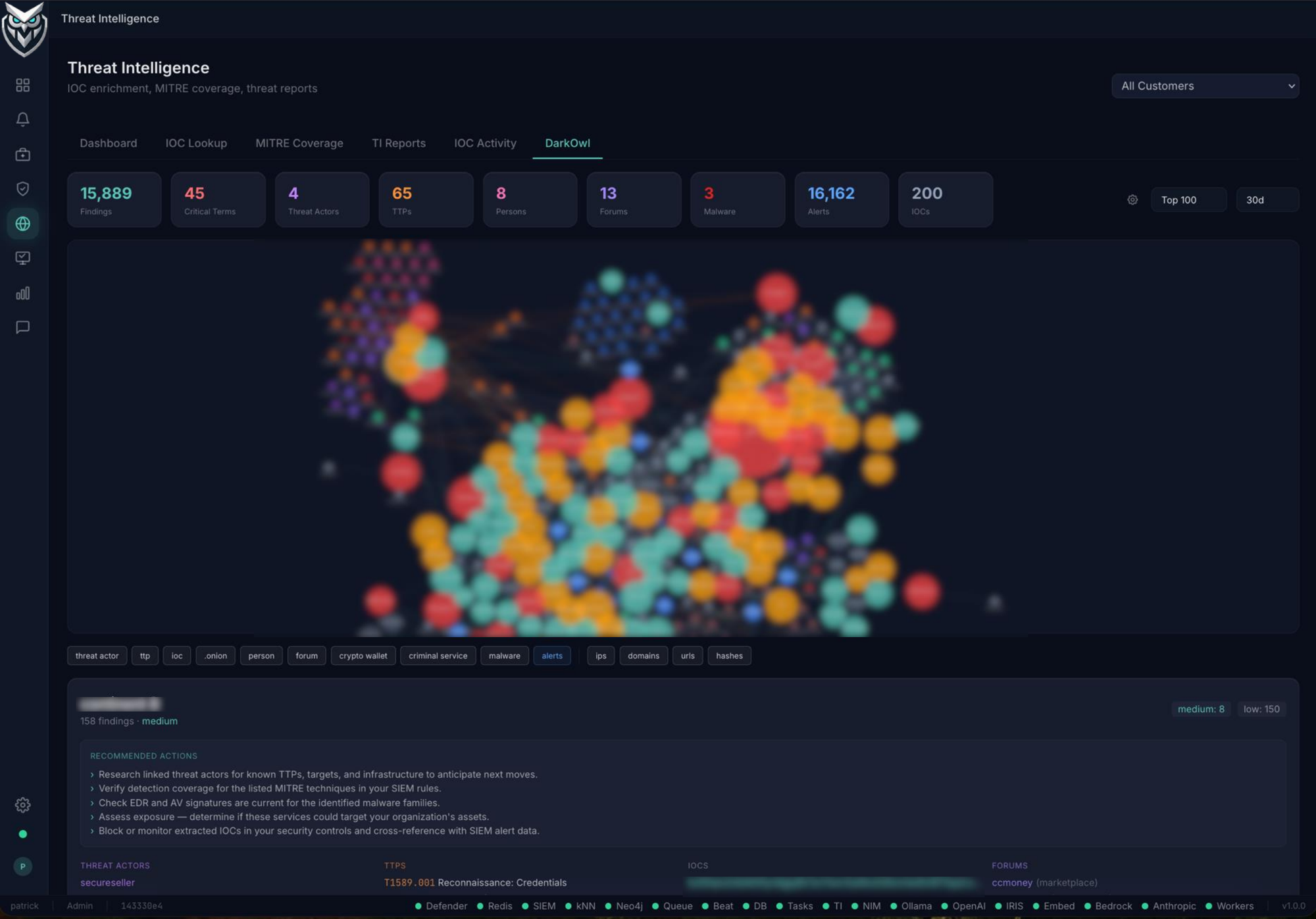
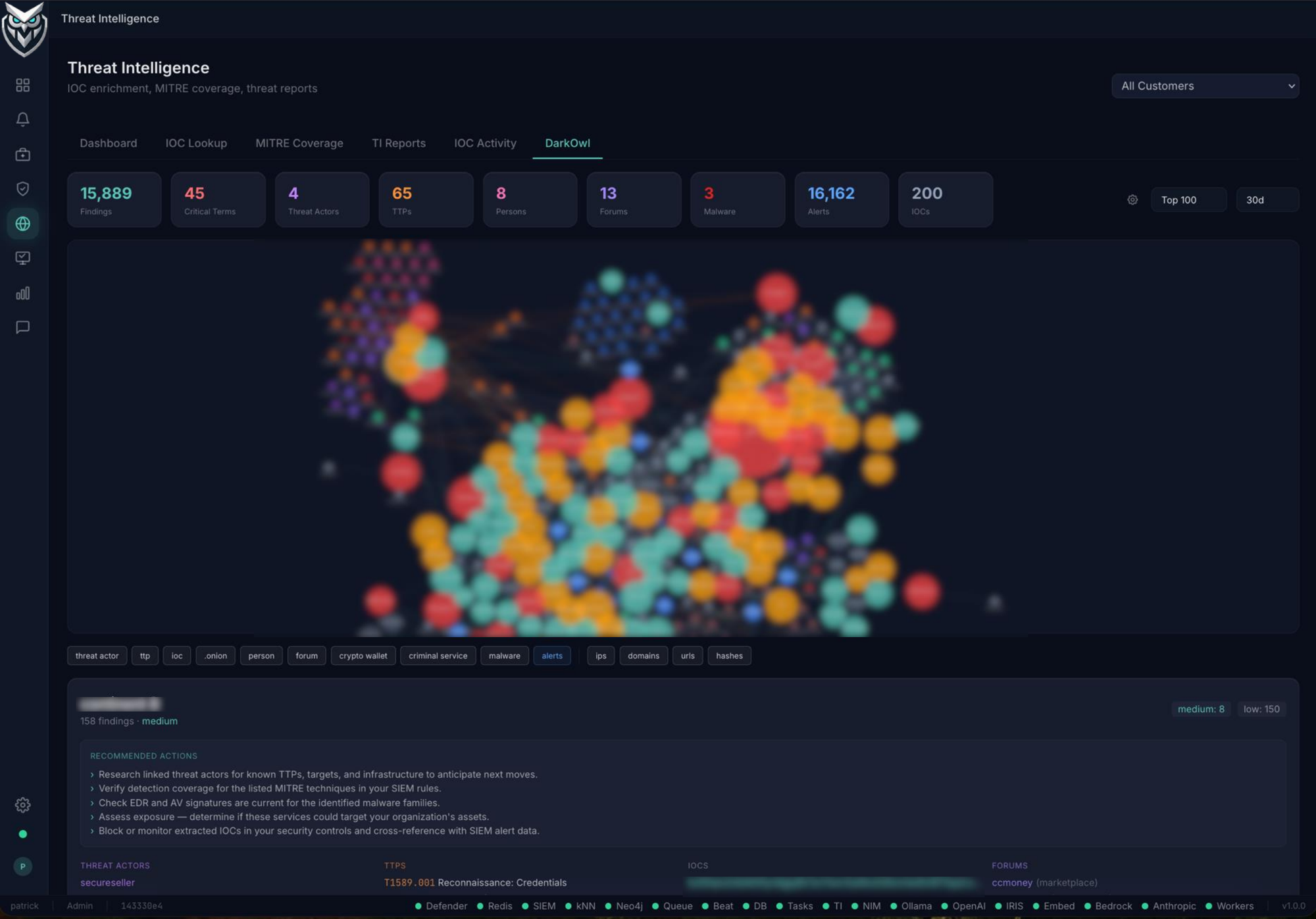
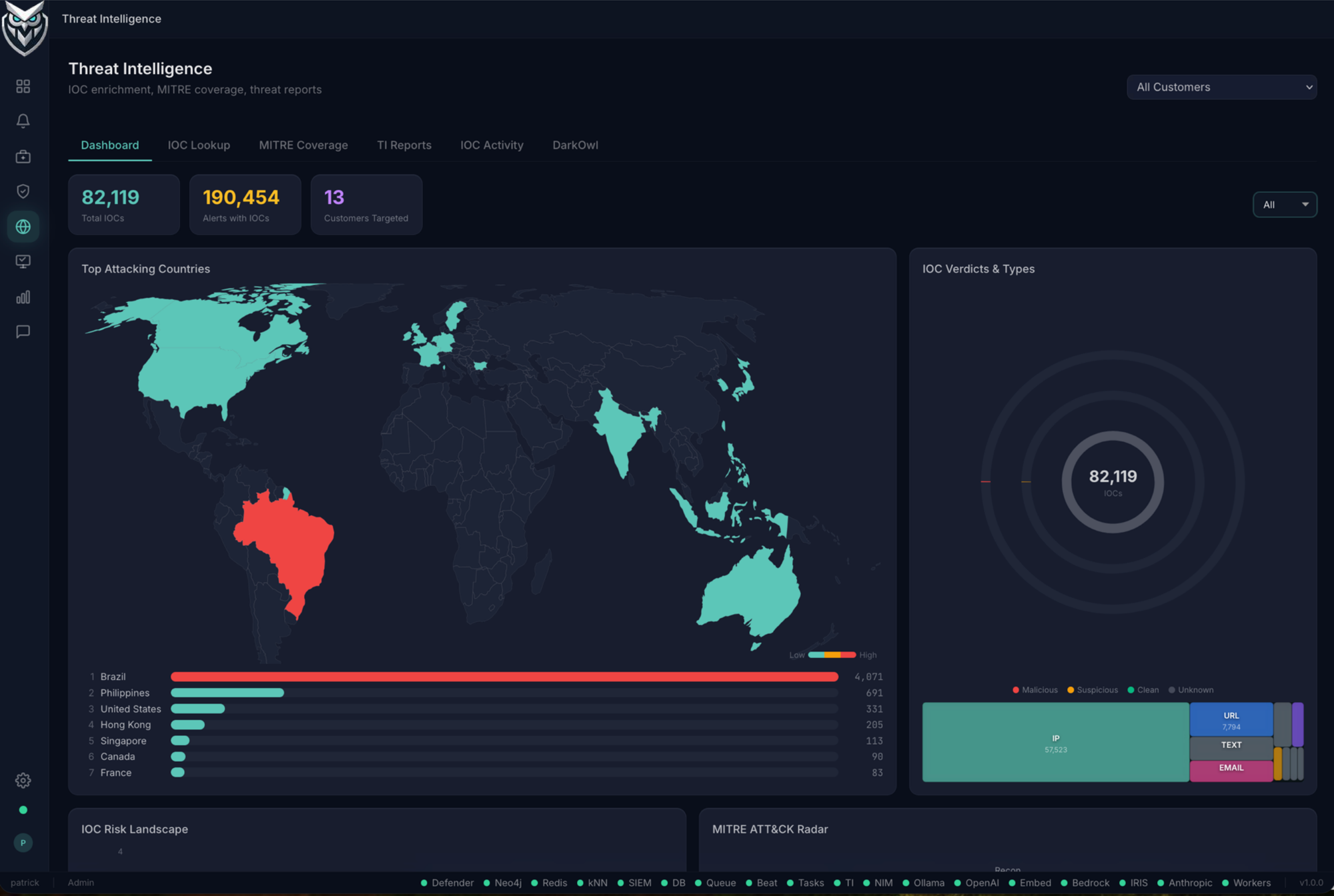
Cross-customer Threat Intelligence